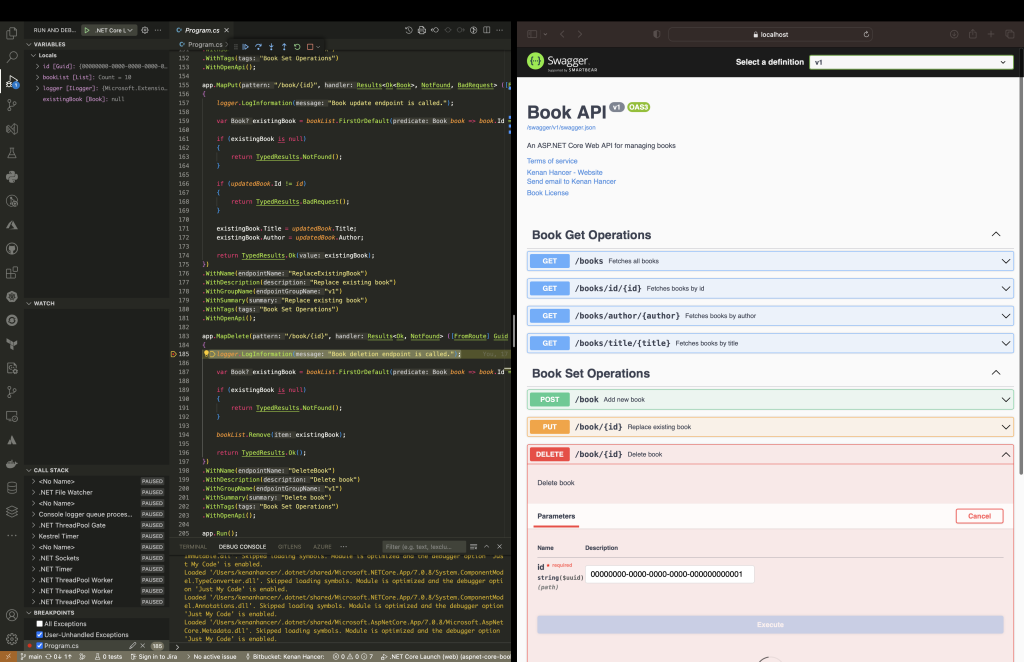
Find project in https://github.com/csharp-projects-kenanhancer/aspnet-core-book-minimal-web-api
Continue readingFind more details in Microsoft scripted installation
dotnet-install
$ curl -sSL https://dot.net/v1/dotnet-install.sh > dotnet-install.sh$ chmod +x dotnet-install.sh$ echo 'export DOTNET_ROOT=$HOME/.dotnet' >> ~/.zshrc
$ echo 'export PATH=$PATH:$DOTNET_ROOT:$DOTNET_ROOT/tools' >> ~/.zshrcfind reference for dotnet-install script reference in dotnet-install script reference
find options for dotnet-install script in dotnet-install script options
Continue reading$ mkdir python_demo
$ cd python_demo$ pyenv local 3.9.16$ pyenv virtualenv 3.9.16 python_demo-3.9.16
# OR pyenv-virtualenv will use local python runtime with the following command
$ pyenv virtualenv python_demo-3.9.16setting pyenv local version to created virtual environment will allow to activate virtual environment automatically when we enter project folder, so exiting from project folder will deactivate virtual environment.
$ pyenv local python_demo-3.9.16$ pyenv activate python_demo-3.9.16$ conda env list
# conda environments:
#
base /opt/homebrew/Caskroom/miniconda/base
python_azure_function_conda_virtual_env-3.9 * /opt/homebrew/Caskroom/miniconda/base/envs/python_azure_function_conda_virtual_env-3.9
python_demo-3.9 /opt/homebrew/Caskroom/miniconda/base/envs/python_demo-3.9
test34-3.9 /opt/homebrew/Caskroom/miniconda/base/envs/test34-3.9
test35-3.9 /opt/homebrew/Caskroom/miniconda/base/envs/test35-3.9
test36-3.9 /opt/homebrew/Caskroom/miniconda/base/envs/test36-3.9$ pyenv virtualenvs
3.10.3/envs/test31-3.10.3 (created from /Users/kenanhancer/.pyenv/versions/3.10.3)
3.10.5/envs/test31-3.10.5 (created from /Users/kenanhancer/.pyenv/versions/3.10.5)
3.10.5/envs/test32-3.10.5 (created from /Users/kenanhancer/.pyenv/versions/3.10.5)
3.11.4/envs/python_demo-3.11.4 (created from /Users/kenanhancer/.pyenv/versions/3.11.4)
3.11.4/envs/test31-3.11.4 (created from /Users/kenanhancer/.pyenv/versions/3.11.4)
3.11.4/envs/test32-3.11.4 (created from /Users/kenanhancer/.pyenv/versions/3.11.4)
3.6.15/envs/test31-3.6.15 (created from /Users/kenanhancer/.pyenv/versions/3.6.15)
3.9.1/envs/test29-3.9.1 (created from /Users/kenanhancer/.pyenv/versions/3.9.1)
3.9.1/envs/test30-3.9.1 (created from /Users/kenanhancer/.pyenv/versions/3.9.1)
3.9.1/envs/test31-3.9.1 (created from /Users/kenanhancer/.pyenv/versions/3.9.1)
3.9.17/envs/python_demo-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
3.9.17/envs/test29-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
3.9.17/envs/test30-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
3.9.17/envs/test31-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
python_demo-3.11.4 (created from /Users/kenanhancer/.pyenv/versions/3.11.4)
python_demo-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
test29-3.9.1 (created from /Users/kenanhancer/.pyenv/versions/3.9.1)
test29-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
test30-3.9.1 (created from /Users/kenanhancer/.pyenv/versions/3.9.1)
test30-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
test31-3.10.3 (created from /Users/kenanhancer/.pyenv/versions/3.10.3)
test31-3.10.5 (created from /Users/kenanhancer/.pyenv/versions/3.10.5)
test31-3.11.4 (created from /Users/kenanhancer/.pyenv/versions/3.11.4)
test31-3.6.15 (created from /Users/kenanhancer/.pyenv/versions/3.6.15)
test31-3.9.1 (created from /Users/kenanhancer/.pyenv/versions/3.9.1)
test31-3.9.17 (created from /Users/kenanhancer/.pyenv/versions/3.9.17)
test32-3.10.5 (created from /Users/kenanhancer/.pyenv/versions/3.10.5)
test32-3.11.4 (created from /Users/kenanhancer/.pyenv/versions/3.11.4)$ ls -lat ~/.local/share/virtualenvs/$ mkdir python_demo
$ cd python_demo$ pyenv local 3.9.6$ pipenv --python $(pyenv which python)$ pipenv --venv$ pipenv install ptvsd -d$ mkdir python_demo
$ cd python_demodon't forget to update name of environment name, and i added
pip,ptvsdpackages to debug azure function.
$ cat > environment.yml <<EOL
name: python_demo-3.9
channels:
- defaults
dependencies:
- python=3.9
- pip
- pip:
- ptvsd
EOL$ conda env create -f environment.yml
Collecting package metadata (repodata.json): done
Solving environment: done
Downloading and Extracting Packages
Preparing transaction: done
Verifying transaction: done
Executing transaction: done
Installing pip dependencies: - Ran pip subprocess with arguments:
['/opt/homebrew/Caskroom/miniconda/base/envs/python_azure_function_conda_virtual_env-3.9/bin/python', '-m', 'pip', 'install', '-U', '-r', '/Users/kenanhancer/Documents/projects/python-projects-kenanhancer/python_azure_function_conda_virtual_env/condaenv.5uk0y5ie.requirements.txt', '--exists-action=b']
Pip subprocess output:
Collecting ptvsd (from -r /Users/kenanhancer/Documents/projects/python-projects-kenanhancer/python_azure_function_conda_virtual_env/condaenv.5uk0y5ie.requirements.txt (line 1))
Using cached ptvsd-4.3.2-py2.py3-none-any.whl (4.9 MB)
Installing collected packages: ptvsd
Successfully installed ptvsd-4.3.2
done
#
# To activate this environment, use
#
# $ conda activate python_azure_function_conda_virtual_env-3.9
#
# To deactivate an active environment, use
#
# $ conda deactivatefind more information in conda
| Task | Conda package and environment manager command | Pip package manager command | Virtualenv environment manager command |
|---|---|---|---|
| Install a package | conda install $PACKAGE_NAME | pip install $PACKAGE_NAME | X |
| Update a package | conda update --name $ENVIRONMENT_NAME$PACKAGE_NAME | pip install --upgrade$PACKAGE_NAME | X |
| Update package manager | conda update conda | Linux/macOS: pip install -Upip Win: python -m pipinstall -U pip | X |
| Uninstall a package | conda remove --name $ENVIRONMENT_NAME$PACKAGE_NAME | pip uninstall $PACKAGE_NAME | X |
| Create an environment | conda create --name $ENVIRONMENT_NAME python | X | cd $ENV_BASE_DIR; virtualenv$ENVIRONMENT_NAME |
| Activate an environment | conda activate $ENVIRONMENT_NAME* | X | source$ENV_BASE_DIR/$ENVIRONMENT_NAME/bin/activate |
| Deactivate an environment | conda deactivate | X | deactivate |
| Search available packages | conda search $SEARCH_TERM | pip search $SEARCH_TERM | X |
| Install package from specific source | conda install --channel $URL $PACKAGE_NAME | pip install --index-url $URL$PACKAGE_NAME | X |
| List installed packages | conda list --name $ENVIRONMENT_NAME | pip list | X |
| Create requirements file | conda list --export | pip freeze | X |
| List all environments | conda info --envs | X | Install virtualenv wrapper, then lsvirtualenv |
| Install other package manager | conda install pip | pip install conda | X |
| Install Python | conda install python=x.x | X | X |
| Update Python | conda update python* | X | X |
Conda is an open-source package management system and virtual environment management system that runs on Windows, macOS, and Linux. It was created for Python programs but it can package and distribute software for any language such as R, Ruby, Lua, Scala, Java, JavaScript, C, C++, FORTRAN.
The two main purposes of Conda are:
While pip can install Python packages, Conda can install packages for any language. Conda packages are binaries, which eliminates the need to compile the code which makes installations faster and more straightforward.
$ brew update
$ brew install --cask miniconda$ conda --version
conda 23.3.1$ conda -h
usage: conda [-h] [-V] command ...
conda is a tool for managing and deploying applications, environments and packages.
Options:
positional arguments:
command
clean Remove unused packages and caches.
compare Compare packages between conda environments.
config Modify configuration values in .condarc. This is modeled after the git config command. Writes to the
user .condarc file (/Users/kenanhancer/.condarc) by default. Use the --show-sources flag to display
all identified configuration locations on your computer.
create Create a new conda environment from a list of specified packages.
info Display information about current conda install.
init Initialize conda for shell interaction.
install Installs a list of packages into a specified conda environment.
list List installed packages in a conda environment.
package Low-level conda package utility. (EXPERIMENTAL)
remove (uninstall)
Remove a list of packages from a specified conda environment. Use `--all` flag to remove all packages
and the environment itself.
rename Renames an existing environment.
run Run an executable in a conda environment.
search Search for packages and display associated information.The input is a MatchSpec, a query language for
conda packages. See examples below.
update (upgrade) Updates conda packages to the latest compatible version.
notices Retrieves latest channel notifications.
options:
-h, --help Show this help message and exit.
-V, --version Show the conda version number and exit.
conda commands available from other packages (legacy):
content-trust
env
Pipenv is a Python tool that aims to bring the best features of multiple other tools into one. It provides an easy way to manage virtual environments and manage package dependencies consistently. Its key goal is to simplify the workflow of managing a Python environment for your project.
$ python -m pip install pipenv$ pipenv --version
pipenv, version 2022.7.4$ pipenv -h
Usage: pipenv [OPTIONS] COMMAND [ARGS]...
Options:
--where Output project home information.
--venv Output virtualenv information.
--py Output Python interpreter information.
--envs Output Environment Variable options.
--rm Remove the virtualenv.
--bare Minimal output.
--man Display manpage.
--support Output diagnostic information for use in
GitHub issues.
--site-packages / --no-site-packages
Enable site-packages for the virtualenv.
[env var: PIPENV_SITE_PACKAGES]
--python TEXT Specify which version of Python virtualenv
should use.
--three Use Python 3 when creating virtualenv.
--clear Clears caches (pipenv, pip). [env var:
PIPENV_CLEAR]
-q, --quiet Quiet mode.
-v, --verbose Verbose mode.
--pypi-mirror TEXT Specify a PyPI mirror.
--version Show the version and exit.
-h, --help Show this message and exit.
Usage Examples:
Create a new project using Python 3.7, specifically:
$ pipenv --python 3.7
Remove project virtualenv (inferred from current directory):
$ pipenv --rm
Install all dependencies for a project (including dev):
$ pipenv install --dev
Create a lockfile containing pre-releases:
$ pipenv lock --pre
Show a graph of your installed dependencies:
$ pipenv graph
Check your installed dependencies for security vulnerabilities:
$ pipenv check
Install a local setup.py into your virtual environment/Pipfile:
$ pipenv install -e .
Use a lower-level pip command:
$ pipenv run pip freeze
Commands:
check Checks for PyUp Safety security vulnerabilities and against
PEP 508 markers provided in Pipfile.
clean Uninstalls all packages not specified in Pipfile.lock.
graph Displays currently-installed dependency graph information.
install Installs provided packages and adds them to Pipfile, or (if no
packages are given), installs all packages from Pipfile.
lock Generates Pipfile.lock.
open View a given module in your editor.
requirements Generate a requirements.txt from Pipfile.lock.
run Spawns a command installed into the virtualenv.
scripts Lists scripts in current environment config.
shell Spawns a shell within the virtualenv.
sync Installs all packages specified in Pipfile.lock.
uninstall Uninstalls a provided package and removes it from Pipfile.
update Runs lock, then sync.
verify Verify the hash in Pipfile.lock is up-to-date.